Keeping The State Of Oklahoma Secure Against A Cyber Attack
Data breaches are common occurrences these days -- hardly a month goes by that we don't hear about a major corporation or a federal government agency being victimized by hackers.Wednesday, July 22nd 2015, 10:56 pm
Data breaches are common occurrences these days -- hardly a month goes by that we don't hear about a major corporation or a federal government agency being victimized by hackers.
So far, however, the state of Oklahoma has managed to avoid a large data breach, but it's certainly not because hackers aren't trying.
Nowhere is that more apparent than in a non-descript basement room at the state's Information Services Division headquarters a few blocks north of the Capitol. There, a world map on a large, wall-mounted video monitor shows dozens of red lines arcing into central Oklahoma from points across the globe.
If Oklahoma City were more of an air traffic hub, it's what a representation of a month's worth of flights into Will Rogers World Airport might look like.
Instead, each line represents an unauthorized attempt to bypass the state's firewall and gain access to secure information. The state's Information Technology experts say they register about 11,000 such attempts each week.
"About 53 percent of endpoints of our state assets are under attack at any given time," said Mark Gower, Oklahoma's chief information security officer.
It's Gower's job to fend them off those attacks.
"Your identity is at risk," said Gower, "based off of the threat of a cyber-attack."
Personal information for just about every person in the state is stored in one or more of the computer systems of Oklahoma's various government agencies. A 6-year plan to consolidate, or unify, those systems is now about two-thirds complete. Unification is putting everyone's sensitive information under one roof, but it’s also making it a lot easier to safeguard that information, officials say.
"Before unification, every agency was responsible for their own security," said Bo Reese, Oklahoma's chief information officer, "they had their own firewalls in place, their own anti-virus or malware."
Reese says it was inefficient, sometimes ineffective, and slow.
"Today, with what Mark has done," said Reese, "we can actually see in real time, and they can respond so quickly."
Gower was hired in January 2013 and quickly got to work on what he does best -- cyber security.
"The system is designed to correlate intelligence," said Gower.
Called CyberWARN, the system evaluates each hit on the firewall, by cross-referencing it with everything from posts on social media, federal intelligence, past history and other variables, and then instantaneously assigns it a threat level.
"A level one is an informational event," explained Gower, "and a level ten is the most high severity event."
A level ten alert triggers an audible siren, and automatically sends a text message to each member of a special response team.
Gower says a level ten attack is dealt with immediately, "by identifying what type of event it was, what type of a system it targeted," and looking at available intelligence to see if it's possible to determine who the attacker was.
Most of the cyber 'events' are not serious threats, but more than a quarter of them -- about 3,000 a week -- are serious enough that they require some sort of follow-up by a member of Gower's team. On average, one to two of them per week are level ten events.
Bo Reese says the goal is, not only to protect the integrity of each agency's web site and operating system, but to keep the personal data of its users from being stolen.
"We know we can't keep every bad actor from gaining access to a system," said Reese, "that's impossible today. But being able to respond quickly and keep the data from leaving the state's control is what's so important."
So far, so good, they say. But continued success, they know, means always trying to stay a step ahead of the hackers.
"We really cannot ever sit back and say we're done," said Gower, "this is always an evolutionary thing."
More Like This
July 22nd, 2015
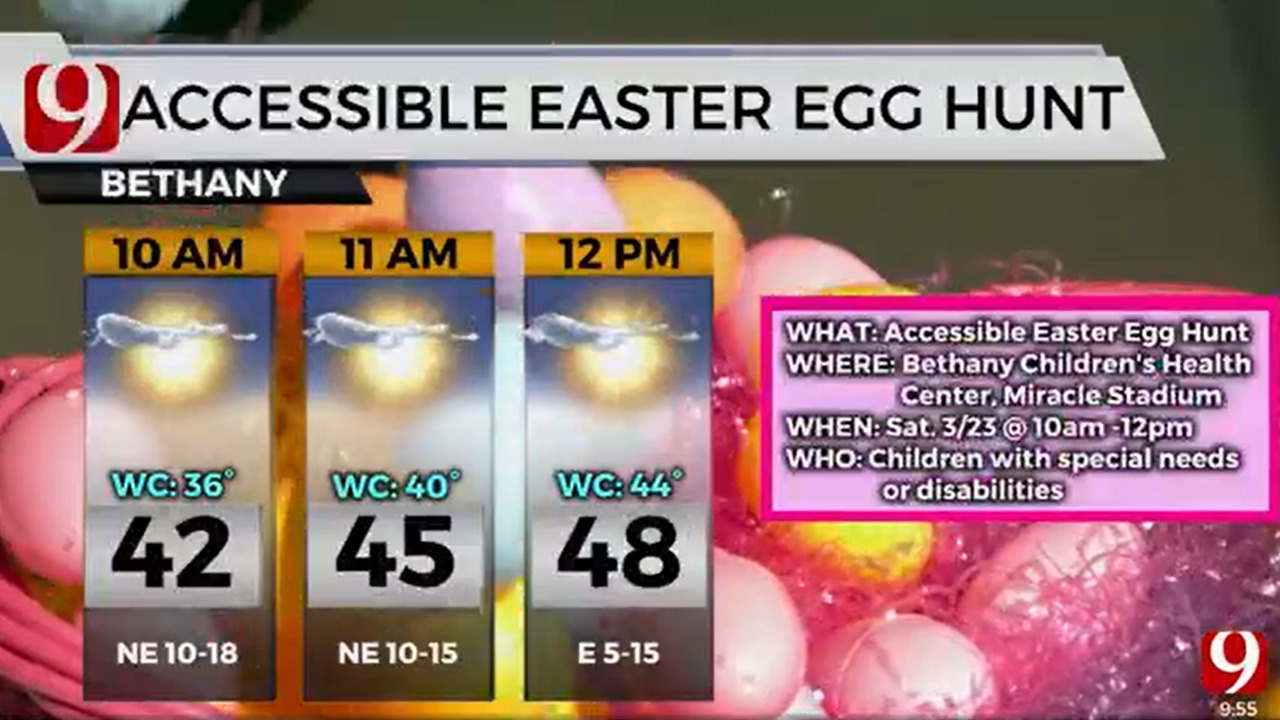
March 22nd, 2024
March 14th, 2024
February 9th, 2024
Top Headlines
May 10th, 2024
May 10th, 2024
May 10th, 2024